This guide explains how to convert a certificate from a provider (such as OVH or Namecheap) into a .pfx file for use in Emby, and how to verify that your private key, CSR, and certificate all match correctly.
This is useful when:
- You purchased an SSL certificate from a provider
- You generated your own CSR
- Emby requires a
.pfxcertificate file - You want to verify everything matches before importing
1. Convert Certificate to PFX Format
Emby requires a .pfx (PKCS#12) certificate file.
Run the following command:
openssl pkcs12 -export -out mgn.pfx \
-inkey mgn_ovh.key \
-in mgn_ovh.crt \
-certfile mgn_ovh.ca-bundle
File Explanation
mgn_ovh.key→ Your private keymgn_ovh.crt→ Certificate issued by providermgn_ovh.ca-bundle→ Intermediate certificate bundlemgn.pfx→ Output file used in Emby
You will be prompted to create a password.
This password will be required when importing into Emby.
2. Troubleshooting: Verify the Key, CSR, and Certificate Match
If Emby refuses the certificate, or conversion fails, ensure that:
- The private key matches the CSR
- The certificate was issued for the correct key
- The CA bundle matches the certificate
All modulus hashes must match.
Confirm the Private Key
openssl rsa -noout -modulus -in mgn_ovh.key | openssl md5
Example output:
MD5(stdin)= xxxxxxxxxxxxxxxxx
Check the Original CSR
openssl req -noout -modulus -in request.csr | openssl md5
The MD5 hash must match the private key output above.
Check the Provider Certificate
openssl x509 -noout -modulus -in mgn_ovh.crt | openssl md5
This must also match the previous two outputs.
If all three hashes match → your key, CSR, and certificate are correctly paired.
3. Verify the Certificate Chain
Ensure the certificate is properly signed by the CA:
openssl verify -CAfile mgn_ovh.ca-bundle mgn_ovh.crt
Expected output:
mgn_ovh.crt: OK
If it returns OK, the certificate chain is valid.
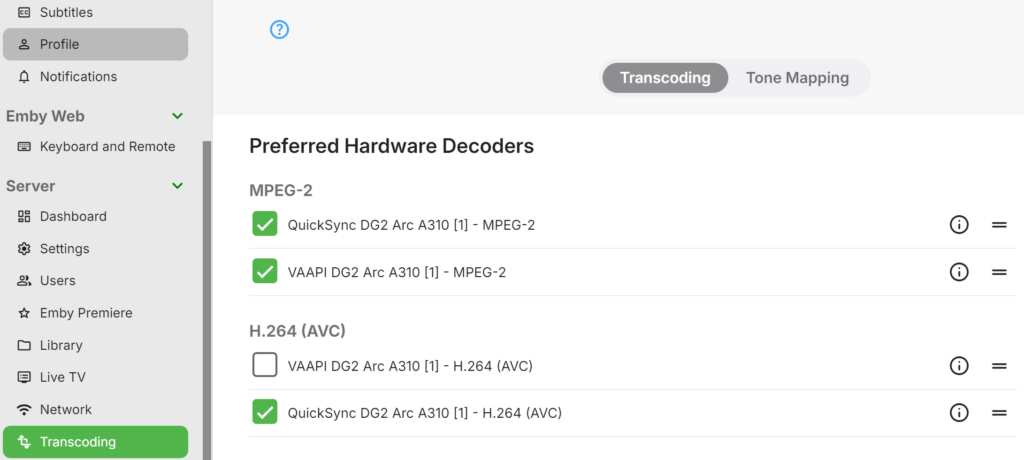
4. Import Into Emby
In Emby:
Dashboard → Network → HTTPS → Certificate Path
Upload the .pfx file and enter the password created during export.
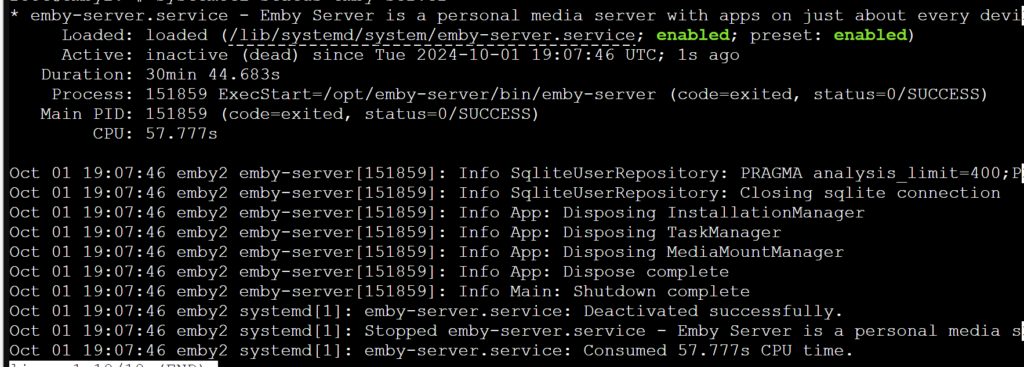
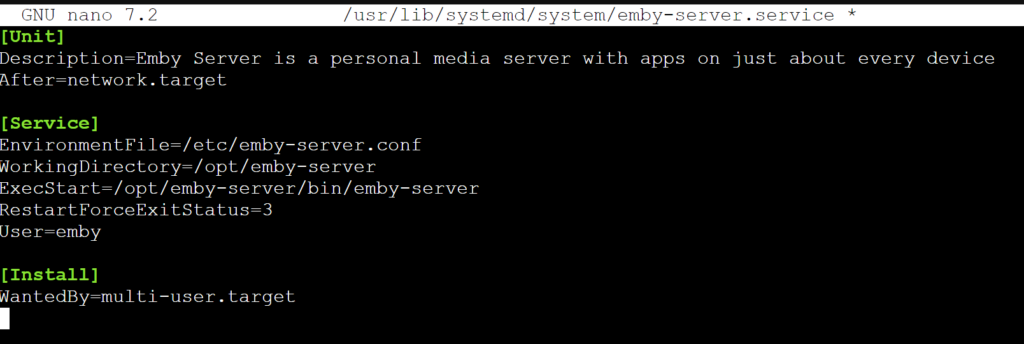
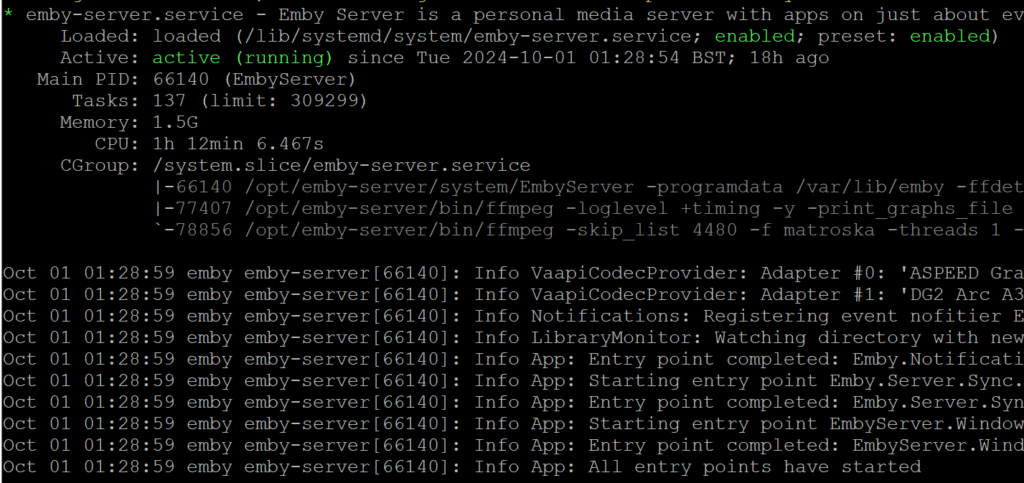
Restart Emby after importing.
Common Issues
- Key does not match certificate → wrong private key used
- CSR regenerated after certificate purchase
- Incorrect CA bundle file
- Missing intermediate certificates
Always confirm modulus values match before attempting conversion.
Tested On
- Debian-based systems
- OpenSSL 1.1 / 3.x
- Emby Server (Linux)
- Certificates from OVH / Namecheap